Phishing isn’t new, and certainly not for Steam accounts. While Steam Guard has been an integral defence since the last major Steam Community upgrade, it still isn’t enough. We take a look at a new method of circumventing Steam Guard and how attackers can gain access to your account.
Analyzing New Steam Account Phishing
Discussion & Analysis
Steam Guard is certainly an improvement over having just a username and password. Checking links and getting the user to verify each click also helps to keep accounts secure as well – but it’s still not enough.
Even when you think your defenses are good enough, someone at some point in time will find a way to breach them. It doesn’t have to be a case of breaking down the front door, but it can also be a case of tricking someone to handing over the keys to the castle. This is what this new method tries to do.
When someone happened to discover and announce that Steam Guard uses files denoted with “ssfn” to store the authentication tokens, they came up with a way to get them. This initial method wasn’t the most intuitive, as it required users to find and manually upload the token “ssfn” file themselves. While this still had some success, someone wanted to improve upon it. The result is what I’m showing and analyzing today.
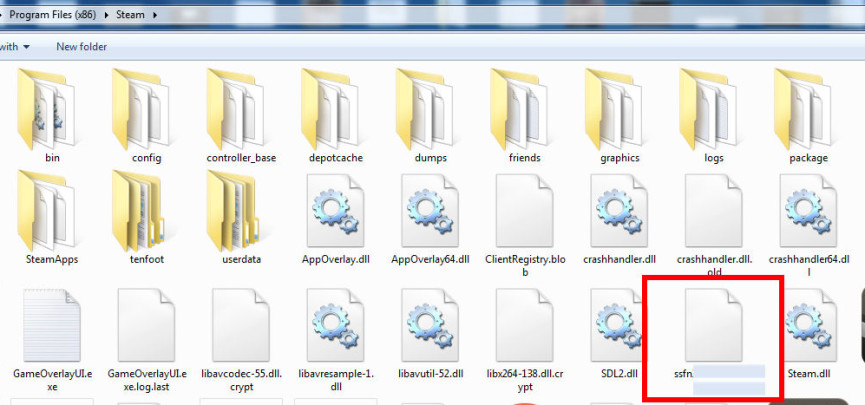
The SSFN file showed by the Malwarebytes blog.
Quite a few “off-the-shelf” hacking products you can acquire today tend to not be open source (meaning one cannot see the code that went into it). That doesn’t mean you can’t find out what kind of damage the product is capable of. Unfortunately, I didn’t have a VM (Virtual Machine) to abuse for testing this sample, so I could only go so far. What I was able to gather from the downloaded portion of the phishing method, was that it was built with the .NET framework. This means that I was able to view and make sense of what was going to happen for the most part.
I did in fact go into more detail in my analysis of this phishing method. I felt that it had become too technical to understand, and trimmed it from the video. You will also see and hear some poor edits, as I was only able to take a single pass on this. The site was “blanked” the next day, more than likely to hide its secrets from security experts and Valve.
Consider this to be a “don’t try this at home” notice. I have the experience, knowledge, and tools to deal with and manage threats like this one. Under no circumstance do I recommend a user to go through the same procedure I did in the video. It is more than likely to end up badly, and I shall not be accountable (along with the publisher of this article) for damages arising from mishandling threats like this one.

No Comments
No comments to display.